Cloud security has become crucial for small business owners and IT professionals who want to stay ahead in today’s digital world. It helps secure significant cloud resources and provides the important tools and techniques to do so.
In 2023, over half of the respondents prioritized preventing cloud misconfigurations, while 12% focused on cloud security training, and 5% aimed to secure Bring Your Own Device (BYOD) policies. ~ Statista
Cloud security involves tracking data, workloads, and architecture changes in multiple cloud computing environments like AWS, Google Cloud, and Azure. It keeps them protected from internal and external attacks.
This guide provides essential knowledge to navigate the complexities of cloud security and secure cloud data.
What is Cloud Security?

Cloud security involves implementing cyber security policies, best practices, and technologies to safeguard applications, data, and infrastructure in cloud environments. It involves protecting storage and networks against threats and managing access. It ensures data governance and the implementation of disaster recovery measures.
Cloud security is important, as the risks associated with cloud computing are ever-increasing. Any organization that utilizes cloud computing must implement a strong set of measures to reduce the risks. Essential measures for any organization include authentication protocols, encryption, access control, network security, and regulatory compliance. Neglecting these measures can have disastrous consequences.
The ultimate goal of cloud security is to provide a secure computing environment that allows organizations to leverage cloud computing while effectively reducing security threats.
How Does Cloud Security Work?
To ensure secure cloud computing, a comprehensive approach that includes various technologies and policies should be implemented to safeguard data, applications, and infrastructure.
- Encryption: Encryption ensures that data remains unreadable even if unauthorized parties gain access. TLS and SSL protocols are used for transmission, while AES algorithms are used for data at rest, ensuring data security.
- Authentication and Access Control: Cloud security involves verifying user and device identities and restricting access to prevent unauthorized access and data breaches in the cloud environment.
- Network Security: Cloud providers use firewalls, VPNs, and IDPS to protect against unauthorized access and malicious activities. They also use segmentation of network resources to isolate sensitive data and applications
- Vulnerability Management: Regular vulnerability assessments and patch management are essential for securing cloud environments. Vulnerability scanning tools identify weaknesses, while automated patch management systems apply security patches promptly.
Cloud Security Challenges
Are you aware of the complexities that come with securing cloud computing environments? Cloud security is a constantly evolving issue. It is influenced by the dynamic nature of cloud computing and the ever-changing threats that come with it.
Some of the challenges include:
- Lack of Visibility and Tracking: Cloud security faces challenges due to a lack of visibility and tracking, especially in distributed data and applications. This can hinder real-time detection of unauthorized access, unusual behavior, and security threats. To address this, monitoring solutions, cloud-native security tools, and proactive security measures are needed.
- Increased Attack Surface: With data and applications accessible over the internet, attackers can exploit vulnerabilities and gain unauthorized access to sensitive information. The use of multiple cloud services and platforms further expands the attack surface.
- Data Breaches: Data breaches can occur due to weak authentication, inadequate access controls, misconfigured cloud services, or insider security threats. It causes financial losses, reputational damage, and legal liabilities for businesses.
- Dynamic Workloads: This allows for flexible resource allocation and management to accommodate varying demand levels and workload patterns. However, this adaptability introduces security risks like misconfigurations, unauthorized access, and vulnerabilities.
- Misconfigurations: Misconfigurations are unintentional settings in cloud services that can lead to security vulnerabilities and expose sensitive data. Common misconfigurations include improper access controls, insecure storage, default password usage, and network settings.
What are the Types of Cloud Security Solutions?
Cloud security solutions are different technologies and services designed to safeguard data, applications, and infrastructure in cloud computing environments.
Here are some of the types of cloud security solutions:
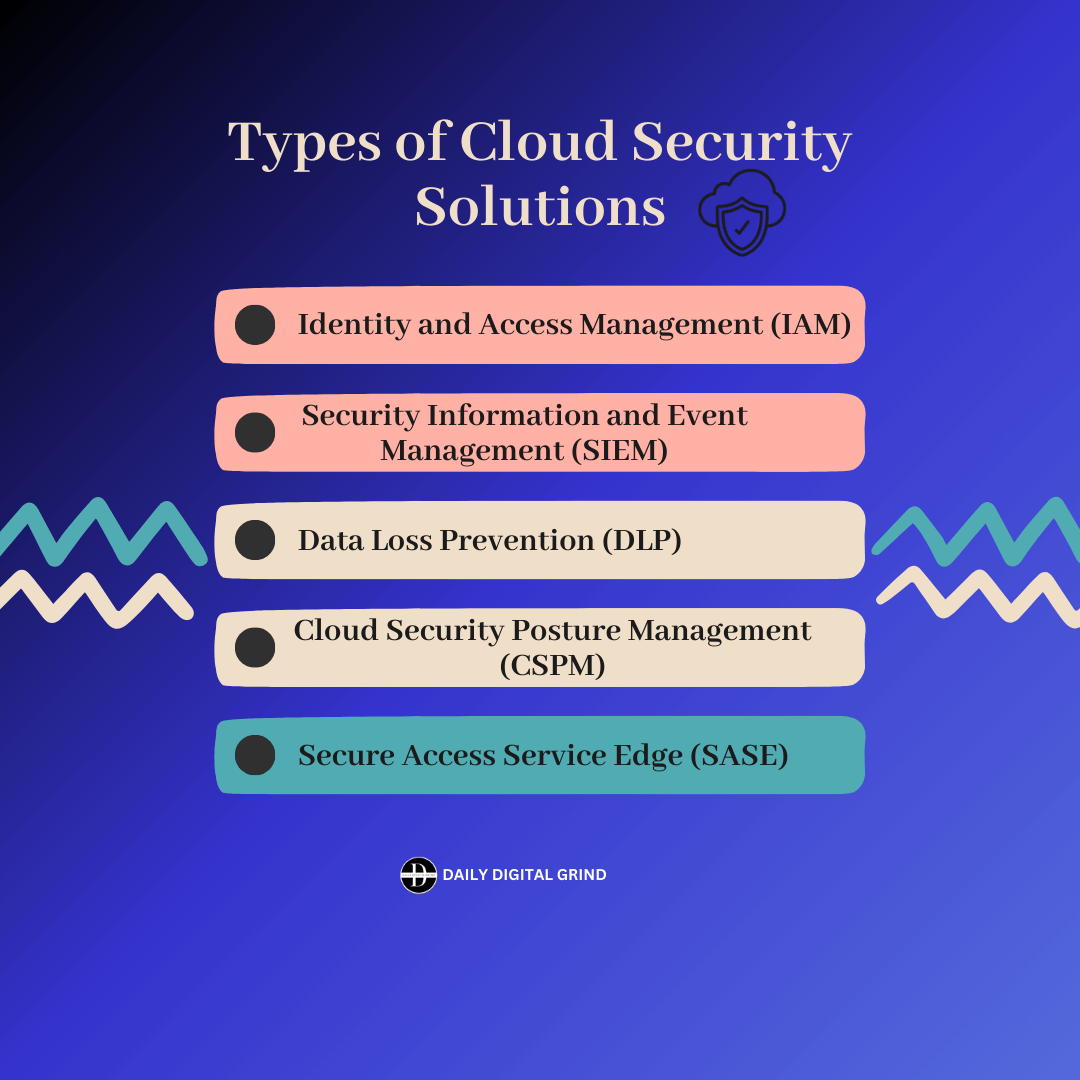
1. Identity and Access Management (IAM)
Identity and Access Management (IAM) is an aspect of cloud security. It ensures that only authorized users have access to resources and data. IAM systems provide centralized management of user accounts, authentication mechanisms, and access policies.
It allows organizations to maintain control over who can access resources. Implementing IAM solutions enhances security, streamlines access management, and reduces data breaches and insider threats in cloud computing environments.
2. Security Information and Event Management (SIEM)
SIEM offers real-time monitoring, threat detection, and incident response capabilities. It collects and analyzes data from cloud services and network devices to identify security threats and anomalies.
SIEM systems can detect suspicious activities like unauthorized access attempts, malware infections, and insider threats. It also facilitates compliance reporting, forensic analysis, and security incident investigation.
3. Data Loss Prevention (DLP)
Data Loss Prevention (DLP) safeguards sensitive data from unauthorized disclosure or loss. DLP solutions monitor, detect, and prevent unauthorized transmission of sensitive information through email, file sharing, and cloud-based applications. They use content inspection, contextual analysis, and policy enforcement techniques to enforce data security policies.
4. Cloud Security Posture Management (CSPM)
Cloud Security Posture Management (CSPM) involves constant reviewing, monitoring, and assuring the security of cloud environments. It helps businesses find and remediate security flaws in their infrastructure, applications, and services.
CSPM solutions give real-time visibility into cloud assets. It allows organizations to enforce security best practices, compliance standards, and governance policies and offers automated tools for configuration management, policy enforcement, and threat detection.
5. Secure Access Service Edge (SASE)
Secure Access Service Edge (SASE) integrates network security functions with WAN capabilities to optimize network traffic. It combines different security technologies like firewall-as-a-service, secure web gateways, cloud access security brokers, and zero trust network access into a unified platform.
SASE provides organizations with secure access to applications and data for remote users and branch offices.
Conclusion
Cloud security is important for modern IT infrastructure to protect data and infrastructure. Organizations can reduce risks like data breaches, unauthorized access, and service disruptions by implementing technologies, processes, and policies.
Organizations must prioritize cloud security to address emerging threats and vulnerabilities. Staying informed about best practices and leveraging the latest security technologies is essential for protecting assets and maintaining customer trust. Investing in strong measures ensures data confidentiality, integrity, and availability. It allows organizations to benefit from cloud computing while managing security risks.
To learn more about cyber security, visit the Daily Digital Grind!
FAQs
Why is cloud security important?
Cloud security prevents threats like data breaches, unauthorized access, and service disruptions. It also reduces risks in dynamic cloud environments and the evolving threat landscape.
What are the 3 categories of cloud security?
The three categories of cloud computing are Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
What are the top cloud security risks?
The top cloud security threats include data breaches, misconfigurations, lack of visibility, data loss, insider threats, data breaches, and many more.